Euler announces 29 audit reports after $4M spent to shore up security
Some vulnerabilities in Euler v2 were found and resolved, and a subsequent $1.25 million bug bounty contest found no vulnerabilities of medium or greater severity.

Crypto lending platform Euler Finance has announced the results of 29 audit reports from 12 different cybersecurity firms regarding its “v2” relaunch. According to the announcement, the reports show that all security issues were resolved. The protocol also held a public $1.2 million post-audit bug bounty that resulted in no medium or higher severity issues being found.
In total, more than $4 million was spent to shore up Euler’s security in anticipation of the relaunch, the announcement stated.
The previous version of Euler was exploited for $195 million in a flash loan attack on March 13, 2023. The attacker subsequently returned all of the funds.
According to the announcement, the new version of Euler “has undergone one of the most expensive and comprehensive security processes for any DeFi protocol to-date.”
Euler’s decentralized autonomous organization, EulerDAO, allocated more than $11 million to the development team in order to develop v2, more than $4 million of which went to security. With these security funds, the team hired new staff tasked with making the protocol adhere to the ISO27001 standards used by banks and defense companies.
Various outside experts were brought in to devise attack vectors and challenge Euler v2’s security. These experts included two security engineers from Web3 security firm Certora, Yield protocol co-founder Alberto Cuesta Cañada and Spearbit security researchers Cmichel and StErMi, among others.
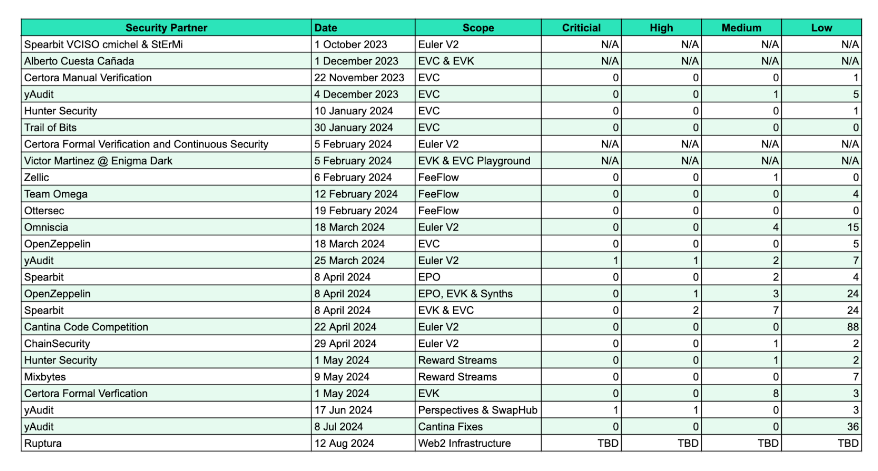
Once the code was completed, the team hired 12 cybersecurity firms to audit each of the Euler modules, and a total of 29 audits have been completed so far.
The auditors included Spearbit, Certora, Hunter Security, Trail of Bits, Zellic, OpenZeppelin, Chain Security, Hunter Security, Omniscia, yAudit, Ruptura and others. The auditors found two critical severity and five high severity vulnerabilities, all of which were subsequently resolved.
When the third-party audits were completed, the team launched a $1.25 million bug bounty contest to help determine if the auditors had missed any vulnerabilities. The bug bounty participants were unable to find any critical, high or medium-severity flaws. The team awarded a total of $200,000 to participants who found low-severity vulnerabilities.
In addition to these security improvements, v2 will provide new features such as customizable vaults, synthetic assets and a fee auction mechanism, according to a blog post the team published on February 22.
Related: Euler Finance attack: How it happened, and what can be learned
The original version of Euler was exploited through a flash loan attack in March 2023. The attacker used two separate accounts. The first account borrowed from the protocol and then used a “donate” function to force itself into default.
Once it was in default, the attacker’s second account liquidated the first one. Because of the generous discounts given to liquidators in Euler v1, the attacker was able to obtain a greater value of assets in the second account than they lost in the first one, allowing them to profit more than $195 million.
Following the attack, the exploiter returned all of the stolen funds just 23 days later. The Euler attack was the largest decentralized finance exploit of 2023.




Responses