SuperEx Educational Series: Understanding Bridge TVL Risk

#TVL #EducationalSeries
In our previous lessons, we took a detailed look at various types of “Bridges.” Today’s topic is also related to bridges — but the main character this time is TVL.
We all know that assets move from one chain to another, liquidity flows across multiple ecosystems, and DeFi, NFT, and GameFi applications operate collaboratively across chains — all of this relies on the existence of bridges.
At the same time, TVL (Total Value Locked) is often seen as a symbol of a project’s strength. But when we combine this perspective with “cross-chain bridges,” TVL is no longer just a growth metric — it becomes a risk amplifier.
In the DeFi context, TVL is often regarded as:
- A symbol of protocol scale
- A reflection of market trust
- An indicator of ecosystem activity
It seems that the higher the TVL, the more successful the project.
But when we apply this logic to cross-chain bridges, things start to become complicated.
Because a bridge is different from a typical DeFi protocol. It is not a yield strategy contract, nor is it an automated market maker pool. It is a security hub that carries the dual responsibility of “asset custody + cross-chain verification.”
In other words: a bridge does not just manage assets — it carries trust.
When more and more assets are locked into bridge contracts, the growth of TVL does not simply represent expansion in scale. It simultaneously means:
- Greater attractiveness as an attack target
- Larger potential losses
- More severe systemic risk
This is exactly what we mean when we say that TVL is also a risk amplifier.
Therefore, when discussing Bridge TVL Risk, the real question is not: “How much value is locked in this bridge?” but rather: “Are these locked assets protected by a sufficiently strong security structure?”
- Click to register SuperEx
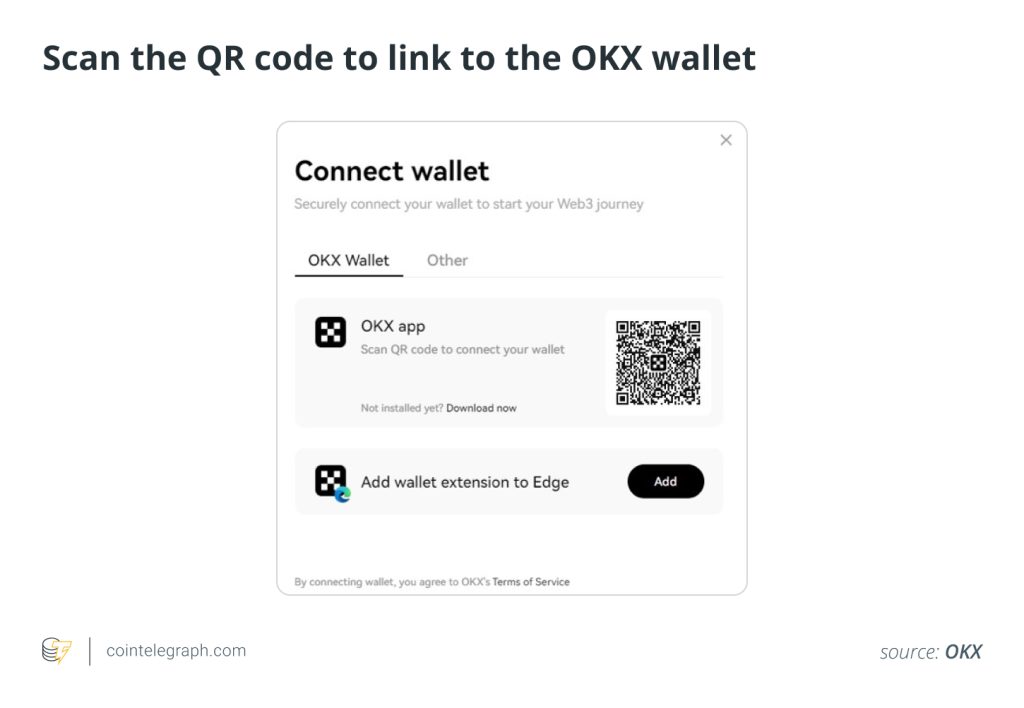
- Click to download the SuperEx APP
- Click to enter SuperEx CMC
- Click to enter SuperEx DAO Academy — Space

What is Bridge TVL Risk?
Bridge TVL Risk refers to the concentrated security risk brought about by the scale of locked assets (TVL) within a cross-chain bridge.
Cross-chain bridges typically adopt a “lock + mint” model:
- Lock real assets on the source chain
- Mint mapped assets on the destination chain
The total amount of assets locked in bridge contracts or validation systems constitutes the TVL.
The problem is that these assets are usually concentrated in a small number of contracts, multi-signature wallets, or validator-controlled networks. Once the security mechanism is breached, an attacker can extract all locked assets in one move.
So, the higher the TVL, the stronger the attack incentive.
Why does TVL become a risk amplifier?
A single high-value target
A bridge essentially resembles a massive “capital pool.” When TVL reaches hundreds of millions or even billions of dollars, the cost of attack becomes severely asymmetric compared to potential returns. Hackers only need one successful attack to gain enormous profit.
This type of risk is “concentrated.”
The security model does not automatically scale with locked value
Many bridges rely on security architectures such as:
- Multi-signature verification
- A small number of validator nodes
- External relay systems
But TVL may grow rapidly as the market expands. If the security strength does not increase in proportion to TVL, risk amplifies exponentially.
Simply put: asset growth is linear, but attack incentives grow exponentially.
Systemic risk from mapped assets
A bridge not only locks assets — it also issues Wrapped Tokens. If a bridge is attacked, especially if locked assets are stolen, the mapped assets lose their peg. At that point, the collateral value in DeFi protocols collapses, and risk spreads from the bridge to the entire ecosystem.
This is systemic risk.
The core issue behind Bridge TVL Risk
At its essence, Bridge TVL Risk is a structural risk caused by “concentrated custody + additional trust layers.”
Cross-chain bridges are usually not part of the underlying consensus. They are intermediary layers attached on top of chains. As long as there exists:
- Private key trust
- Validator trust
- Smart contract implementation trust
- Economic security assumptions
TVL will amplify the fragility of these assumptions.
How to reduce TVL risk?
The core problem of Bridge TVL Risk lies in the fact that assets are highly concentrated, but the security structure does not necessarily strengthen proportionally. Therefore, the key to reducing TVL risk is not to “limit growth,” but to dynamically match security capability with asset scale.
Let’s further expand on four core directions.
Limit the TVL cap of a single bridge
Setting exposure limits for a bridge is the most direct and effective control measure. This may include:
- Daily cross-chain transfer limits
- Maximum per-transaction limits
- Total locked asset caps
- Risk-tiered limits (different caps for different asset categories)
The logic is simple: even if an attack occurs, losses remain within a controllable range.
This is similar to “risk exposure management” in traditional finance.
If a bridge has no cap mechanism and TVL can grow without limit, once its security is breached, losses will be “fully released.” A reasonable TVL cap is essentially a defensive design against extreme events.
Adopt native interoperability protocols
Many bridges rely on:
- Multi-signature verification
- Relay servers
- External validator nodes
These models essentially introduce additional trust layers. In comparison, native interoperability protocols are more robust.
For example:
- Cross-chain models based on light client verification
- Consensus-level validation structures
- Shared security networks
In the Cosmos ecosystem, IBC (Inter-Blockchain Communication) enables large-scale cross-chain communication without custody by allowing chains to directly verify each other’s block headers.
Similarly, Polkadot’s relay chain provides shared security, allowing cross-chain security to inherit from the main chain’s consensus. The advantage of such architectures is that security originates from consensus itself, rather than an additional validation layer.
When security is bound to underlying consensus, TVL growth does not simply amplify trust assumptions.
Strengthen decentralized validation
TVL risk is fundamentally related to “attack cost.” If a bridge’s validation structure is overly concentrated, such as:
- 5 multi-signature nodes
- Control by a small number of operators
- Low staking thresholds
Then the attack cost is relatively low.
Improving security can be approached from three dimensions:
- Increase the number of validator nodes
- Raise staking thresholds
- Introduce slashing or penalty mechanisms
When attackers must control a large number of nodes or pay a high economic price, the ratio between attack reward and cost becomes rebalanced.
Security is not absolute defense — it is about increasing the difficulty of attack.
Dynamic risk management mechanisms
This is an important direction for future bridge design. Traditional bridges often have fixed security rules and static parameters, while TVL changes dynamically.
Therefore, “TVL-triggered security enhancement mechanisms” can be introduced:
- When TVL grows beyond a certain scale → increase signature thresholds
- When TVL exceeds a risk zone → extend confirmation periods
- When TVL spikes suddenly → activate manual review mechanisms
This mechanism is similar to liquidity risk control systems in banks. When risk exposure expands, the security level automatically increases.
Additionally, it can be combined with:
- Real-time risk scoring
- Abnormal behavior monitoring
- Automatic pause mechanisms
So that the bridge can quickly enter protection mode when anomalies are detected.
Conclusion: Make security scalable
The core of reducing TVL risk is not about reducing assets, but about making the security structure scalable.
When TVL grows:
- Validation strength should increase accordingly
- Attack costs should rise accordingly
- Risk exposure should be reasonably limited
As connectors in the multi-chain era, cross-chain bridges must shift from “function-first” to “security-first.” Because in the world of bridges, TVL is not just a badge of honor — it is a stress test of security commitments.






Responses