Io.net responds to GPU metadata attack
The founder of Io.net will host a livestream on April 28 to demonstrate live cluster creation and rest the fear, uncertainty and doubt.

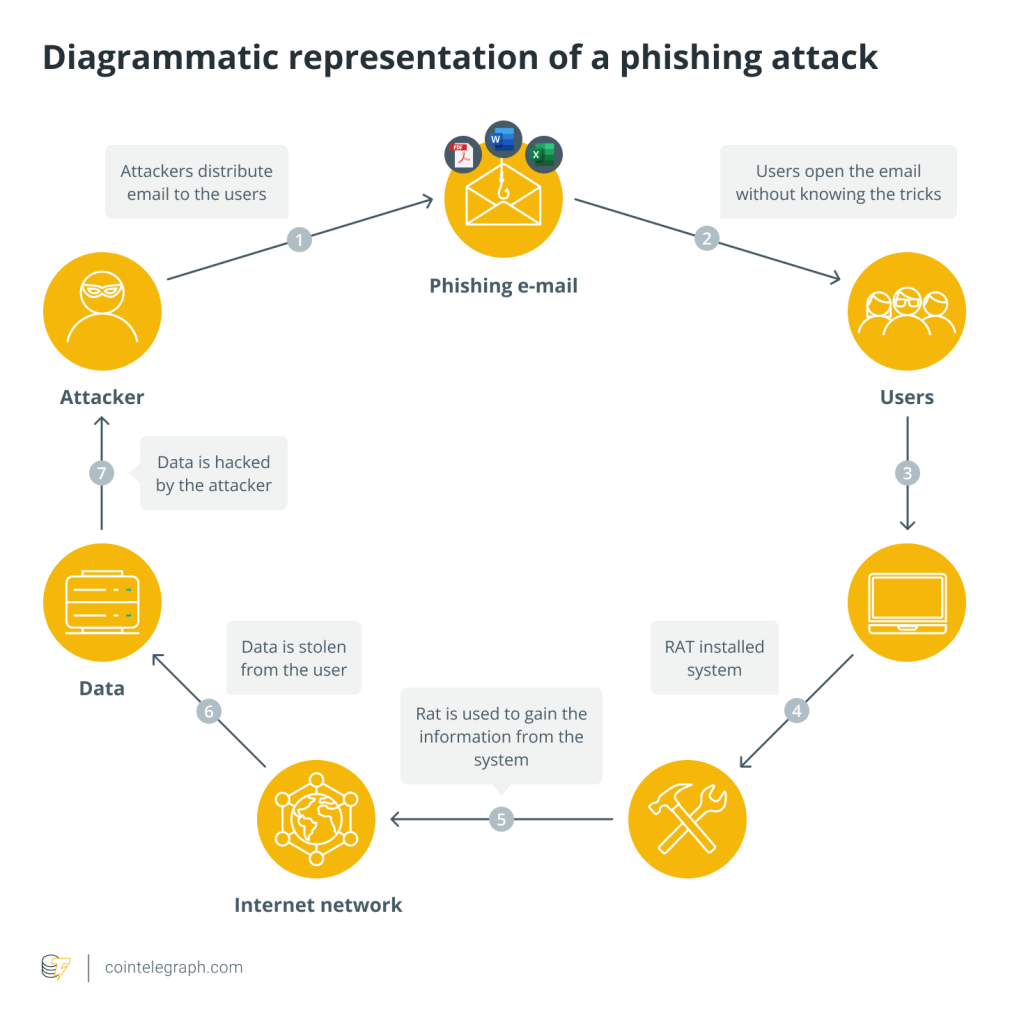
Io.net, a decentralized physical infrastructure network (DePIN), recently experienced a cybersecurity breach. Malicious users exploited exposed user ID tokens to execute a system query language (SQL) injection attack, which led to unauthorized changes in device metadata within the graphics processing unit (GPU) network.
Husky.io, Io.net’s chief security officer, responded promptly with remedial actions and security upgrades to protect the network. Fortunately, the attack did not compromise the GPUs’ actual hardware, which remains secure due to robust permission layers.
The breach was detected during a surge in write operations to the GPU metadata API, triggering alerts at 1:05 am PST on April 25.
In response, security measures were reinforced by implementing SQL injection checks on application program interfaces (APIs) and enhancing the logging of unauthorized attempts. Additionally, a user-specific authentication solution using Auth0 with OKTA was swiftly deployed to address vulnerabilities related to universal authorization tokens.
Unfortunately, this security update coincided with a snapshot of the rewards program, exacerbating an expected decrease in supply-side participants. Consequently, legitimate GPUs that did not restart and update could not access the uptime API, causing a significant drop in active GPU connections from 600,000 to 10,000.
To address these challenges, Ignition Rewards Season 2 has been initiated in May to encourage supply-side participation. Ongoing efforts include collaborating with suppliers to upgrade, restart, and reconnect devices to the network.
The breach stemmed from vulnerabilities introduced while implementing a proof-of-work (PoW) mechanism to identify counterfeit GPUs. Aggressive security patches before the incident prompted an escalation in attack methods, necessitating continuous security reviews and improvements.
Related: AI has a hardware crisis: Here’s how decentralized cloud can fix it
The attackers exploited a vulnerability in an API to display content in the input/output explorer, inadvertently revealing user IDs when searching by device IDs. Malicious actors compiled this leaked information into a database weeks before the breach.
The attackers leveraged a valid universal authentication token to access the ‘worker-API,’ enabling changes to device metadata without requiring user-level authentication.
Husky.io emphasized ongoing thorough reviews and penetration tests on public endpoints to detect and neutralize threats early. Despite challenges, efforts are underway to incentivize supply-side participation and restore network connections, ensuring the platform’s integrity while serving tens of thousands of compute hours per month.
Io.net planned to integrate Apple silicon chip hardware in March to enhance its artificial intelligence (AI) and machine learning (ML) services.





Responses